NFC business cards are generally safe for professional networking because they usually share only a secure web link, not personal data. Most risks come from malicious links, tag tampering, or weak privacy controls. You can reduce these risks by using HTTPS links, locked NFC tags, and platforms that provide built-in privacy protection.
For example, eylet uses factory-locked NFC tags that prevent reprogramming and, if opted, includes a Privacy Wall that requires visitors to enter a user-defined 4-digit PIN before viewing profile details. This design helps block unauthorized access, accidental NFC taps, and online scanning abuse. Source: eylet Privacy Wall documentation
What happens when you tap an NFC business card?
When you tap an NFC business card, your smartphone reads a small data record stored inside the NFC chip. In most cases, this record contains only a web link to a digital profile. Your phone then opens that link in the browser.
What data is actually shared?
In most deployments, the NFC chip contains:
- A secure URL to a digital profile
- Occasionally, a digital contact card (vCard)
It does not automatically share:
- Your contacts
- Your messages
- Your photos
- Your location
- Your payment credentials
Any additional data exchange happens only after you intentionally interact with the profile page.
Are NFC business cards safe?
In real-world professional use, experts consider NFC business cards safe when teams deploy them correctly. Most security concerns relate to link manipulation, unsecured NFC tags, and social engineering, not the NFC protocol itself.
Cybersecurity researchers have documented that attackers can rewrite unlocked NFC tags to redirect users to phishing websites.
Key point
NFC safety is mostly “link safety.” If you trust the destination and protect the tag from tampering, you remove most real-world risk.
Key risks to understand (and how to reduce them)
Most real-world NFC risks are operational, not technical. Understanding these helps you deploy cards safely, especially when you share them at events or in busy public spaces.
1) Malicious link redirection
If someone replaces or tampers with an NFC tag, a tap could redirect to a phishing site. This type of attack mirrors the risk you face when clicking unsafe email links or scanning compromised QR codes.
How to reduce risk:
- Use HTTPS links
- Use a branded domain, so people recognize what they’re opening
- Verify link previews before opening
- Avoid tapping unknown or damaged tags
2) NFC tag rewriting
Some NFC tags remain rewritable unless permanently locked. Developers widely recommend locking tags after programming to prevent unauthorized overwriting.
How eylet reduces this risk (verified): eylet NFC cards use factory-locked NFC tags that prevent reprogramming. Factory locking blocks attackers from overwriting the stored destination link and redirecting taps to malicious websites. Source: eylet getting started digital cards
3) Phishing through social engineering
Attackers sometimes place fake NFC stickers or QR codes on public surfaces to trick people into opening malicious links. If the destination looks unfamiliar, avoid opening the link.
How to reduce risk:
- Prefer official branded cards and signage
- Ask staff to verify the domain before opening
- Train your team to treat taps and scans like links
NFC vs QR code security
Neither NFC nor QR codes are inherently safer. Both typically open web links. Security depends on link control, platform trust, and good deployment habits.
In practice:
- NFC requires close, intentional interaction, which can reduce accidental triggers.
- QR is visible, and many cameras show a destination preview before opening.
If you want a simple, reliable setup, use NFC with a QR fallback pointing to the same HTTPS profile link.
Privacy: what actually matters
The NFC chip rarely poses a privacy risk on its own. The real privacy surface is your digital profile. If you publish personal phone numbers, email addresses, or addresses on your profile, anyone with the link can view them.
Practical privacy practices
- Use business contact channels instead of personal ones
- Limit what you show publicly and keep sensitive fields private
- Use access controls when you share at large events
- Monitor traffic for unusual spikes
Verified: eylet Privacy Wall and PIN protection
eylet includes a built-in Privacy Wall that blocks profile viewing unless a visitor enters a user-defined 4-digit PIN. The documentation states that this helps prevent unauthorized viewing, accidental NFC taps, and online scanning abuse. It also says you can enable, disable, or modify the Privacy Wall settings at any time. Source: eylet Privacy Wall documentation
Why this matters at events
When people tap quickly at trade shows, a PIN gate can prevent accidental exposure of contact details. It also helps if someone shares your profile link beyond the original context.
NFC safety for trade shows, exhibitions, and field teams
Busy environments increase accidental taps and scanning. They also create opportunities for link tampering if your signage is unattended. You can reduce risk by standardizing how your team shares and by using locked tags and privacy controls.
Event-safe setup:
- Use branded domains and HTTPS links
- Prefer factory-locked tags for long-term deployments
- Enable PIN protection for contact details
- Train staff to verify the link preview before opening
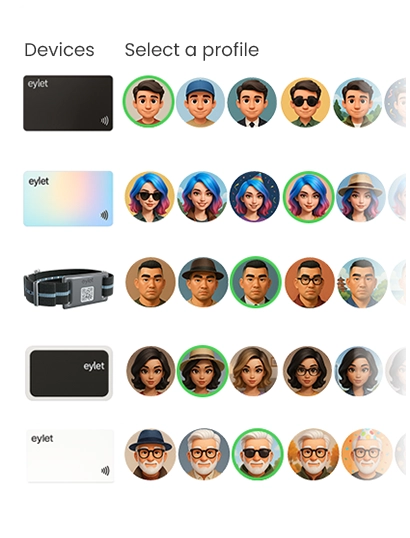
If you manage multiple staff members, you also want clear onboarding and centralized controls. eylet publishes a Teams Getting Started guide that describes team onboarding and centralized management. Source: eylet teams getting started
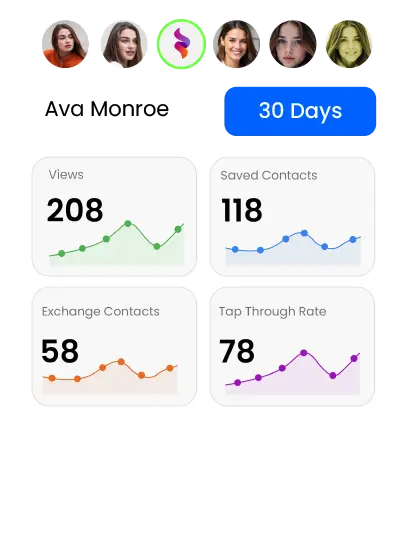
Lead capture and analytics: security with visibility
Analytics help you understand what works, but they also add responsibility. Keep analytics focused on engagement signals, and avoid collecting unnecessary sensitive data.
eylet’s product pages reference analytics and reporting-style insights for engagement, and its official app listing describes built-in statistics and analytics for views and link clicks. Sources: eylet.com
Pricing models and security governance
Security is not only technical. It is also governance. If your pricing model makes team rollouts painful, you may end up with inconsistent profiles and weak processes.
Model: What it often means in practice
| Free | Basic use, branding limits, fewer controls, upgrade pressure |
|---|---|
| Subscription | Admin tools, but recurring per-user costs that grow with headcount |
| One-time purchase | Predictable budgeting, easier scaling for teams and event staff |
eylet publicly positions itself as “No Subscriptions, No App Fees,” which may appeal if you want predictable long-term costs for staff rollouts. Source: eylet.com
Teams: managing privacy at scale
Most privacy failures happen when teams lack consistent rules. A safer rollout uses templates, clear permissions, and standardized lead handling.
- Use centralized templates so staff share consistent information
- Assign editing permissions so only the right people can change key fields
- Standardize lead capture so data stays organized
eylet’s team documentation covers onboarding and centralized team management. Source: eylet teams getting started
Final checklist: Are NFC business cards safe for you?
- Technical safety: HTTPS links, branded domains, and locked NFC tags
- Privacy controls: limit what shows publicly and use PIN protection when needed
- Team governance: templates, roles, and consistent lead workflows
eylet verification: eylet provides factory-locked NFC tags that cannot be reprogrammed, along with a Privacy Wall with a user-defined 4-digit PIN to help prevent unauthorized viewing, accidental NFC taps, and online scanning abuse. Source: eylet getting started digital cards
FAQ
Are NFC business cards safe?
Yes, when you use secure links, protect tags from tampering, and control what your profile displays. Source: NFC Forum
Can NFC business cards be hacked?
The most common risk is link tampering through rewritable tags or sticker swaps. Locked tags and link verification reduce this risk.
Do NFC business cards store personal data?
Most store a URL or a basic contact reference. Your privacy risk depends on what you publish on the profile page.
Is NFC safer than QR codes?
Both usually open a link. Safety depends on the destination and your verification habits, not the format.
Do I need an app to use an NFC business card?
Many systems open a browser-based profile without requiring the visitor to install an app. eylet’s app listing states the recipient does not need an app.